As we move into the second half of 2026, the “Password Era” is officially entering its twilight. The centralized “Login with Google” or “Sign in with Apple” buttons that dominated the last decade are being challenged by a more secure, privacy-centric alternative: Decentralized Identity (DID). Driven by the need to combat AI-generated deepfakes and the constant threat of corporate data breaches, DID is transforming from a Web3 niche into the primary way we verify our humanity and credentials online.
How do you prove you are human in a world of 2026-grade AI? As the “Dead Internet Theory” becomes a localized reality, Decentralized Identity has emerged as the definitive standard for Proof of Personhood. This comprehensive report on DID and the end of traditional logins provides a data-driven look at the rise of “Sybil-resistant” protocols. From World ID’s global biometric standard to the decentralized reputation scores of Gitcoin Passport, we analyze how the 2026 web is being rebuilt on a foundation of verifiable, decentralized trust.
CHECK: How AI Enhances Cybersecurity in Web3: Best Practices for 2026
This analysis tracks the integration of W3C Decentralized Identifier standards into mainstream browsers and operating systems. We break down the Top DID Protocols of 2026, including ENS (Ethereum Name Service) and Veramo, which are enabling a “Single Sign-On” (SSO) experience that is mathematically impossible to hack. For businesses, the transition to DID means zero liability for stored passwords and a 90% reduction in account takeover fraud, making it the most important cybersecurity upgrade of the decade.
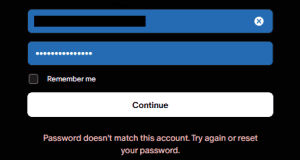
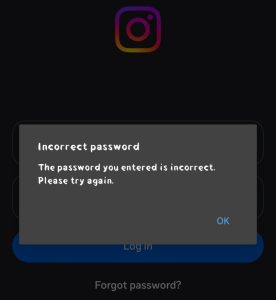
Password fatigue is real. In 2026, the average person manages over 100 online accounts, resets forgotten passwords multiple times per month, and lives with the constant background anxiety of data breaches. Major hacks continue to expose millions of credentials every year, while centralized identity providers harvest and monetize personal data with little transparency.
What if you could prove who you are online without ever sharing your password, email, or personal details again? What if one secure digital identity worked seamlessly across websites, apps, banks, governments, and decentralized platforms — giving you full control while dramatically improving security and privacy?
This is the promise of Decentralized Identity (DID) and Self-Sovereign Identity (SSI). In 2026, the technology has moved from concept to early mainstream pilots, with major platforms, governments, and enterprises actively testing and deploying solutions that could eventually replace traditional username-and-password systems entirely.
This in-depth guide explores how decentralized identity works, why it has the potential to fundamentally replace legacy login systems, real-world progress in 2026, key benefits and challenges, leading projects, and what the transition to a passwordless future might look like.
The Broken Reality of Traditional Logins
Traditional identity systems suffer from systemic flaws:
- Centralization Risks: One breach at a major provider can compromise millions of accounts.
- Password Fatigue: Users reuse weak passwords or rely on password managers that become single points of failure.
- Privacy Erosion: Companies collect far more data than needed for authentication.
- Exclusion: Billions of people lack easy access to traditional identification documents.
- Poor User Experience: Forgotten passwords, two-factor fatigue, and account recovery nightmares.
These problems create friction, drive abandonment, increase fraud, and cost businesses billions in lost revenue and support expenses annually.
Decentralized Identity offers a fundamentally different approach.
What Is Decentralized Identity (DID) and Self-Sovereign Identity?
Decentralized Identity allows individuals and organizations to create and control their own digital identities without relying on any central authority.
Self-Sovereign Identity (SSI) takes this further: you own and control your identity data. You decide what to share, when to share it, and can revoke access instantly — all while cryptographically proving claims without revealing unnecessary information.
Core technical components include:
- Decentralized Identifiers (DIDs): Unique, globally resolvable identifiers that point to cryptographic public keys and metadata. They don’t depend on any single company.
- Verifiable Credentials (VCs): Tamper-proof digital documents (like a digital passport, degree, or driver’s license) that can be shared selectively.
- Zero-Knowledge Proofs (ZKPs): Prove a claim (e.g., “I am over 18”) without revealing the underlying data.
- Blockchain or Distributed Ledgers: Provide anchors for trust and immutability without storing sensitive personal data on-chain.
How Decentralized Identity Actually Works in Practice
- You create a digital wallet that holds your private keys and identity documents.
- Issuers (universities, governments, banks) issue verifiable credentials to your wallet.
- When logging into a service, you present a selective disclosure proof (e.g., “This account belongs to someone verified by Bank X”).
- The verifier checks the cryptographic proof against the issuer’s public keys — no passwords or central database lookups needed.
The entire process can happen in seconds, with far greater security and privacy than current systems.
Current State of Decentralized Identity in 2026
Adoption has accelerated significantly:
- Major tech companies and consortia support DID standards (W3C DID specification is now mature).
- Governments in Europe, Asia, and parts of Africa are running large-scale SSI pilots for digital IDs and cross-border services.
- Web3 platforms widely use wallet-based logins (e.g., “Connect Wallet” as a primary login method).
- Enterprise solutions for employee credentials, KYC, and supply chain verification are in production.
- Privacy-preserving age and credential verification is becoming common in gaming, social, and adult platforms.
While full replacement of passwords is still years away, decentralized identity is already the default experience in many Web3 applications and is making serious inroads into traditional sectors.
Major Benefits That Could Drive Replacement of Traditional Logins
Superior Security No central database of credentials to steal. Compromising one account doesn’t affect others. Cryptographic proofs are extremely difficult to forge.
Enhanced Privacy Share only the minimum information required. Services never see your full data or store it long-term.
Better User Experience One identity across thousands of services. No more password resets. Seamless recovery through social recovery or hardware keys.
Inclusivity People without traditional IDs (refugees, unbanked populations) can build portable digital reputations.
Interoperability A single identity works across Web2, Web3, government services, and enterprises.
Reduced Fraud Verifiable credentials make synthetic identity fraud and account takeovers much harder.
Compliance Advantages Built-in support for GDPR, data minimization, and selective disclosure helps organizations meet regulatory requirements more easily.
Leading Projects and Platforms in 2026
- Polygon ID — Strong enterprise and Web3 adoption with zero-knowledge capabilities.
- Worldcoin / World ID — Controversial but high-visibility iris-based proof-of-personhood system.
- DID:Web and DID:Key — Lightweight standards seeing broad developer adoption.
- Veramo and SpruceID — Developer toolkits making integration easier.
- Government-Backed Systems — European Digital Identity Wallet pilots, various national SSI projects.
- Web3-Native Solutions — ENS (Ethereum Name Service), Lens Protocol (decentralized social identity), and various wallet-based systems.
Real-World Use Cases Gaining Traction

- Web3 dApps — Wallet connection as the primary (and often only) login method.
- Banking and Fintech — Reusable KYC across multiple platforms.
- Healthcare — Portable medical records with patient-controlled sharing.
- Education — Verifiable degrees and certifications that employers can instantly validate.
- Travel and Border Control — Digital passports and selective credential sharing.
- Gig Economy — Portable reputation and work history across platforms.
- Social Media — Censorship-resistant, portable identities and communities.
Challenges and Barriers to Mass Adoption
Technical Complexity Managing private keys and recovery mechanisms remains difficult for non-technical users.
Interoperability Issues Different DID methods and credential formats still create fragmentation.
Regulatory Hurdles Governments must align on standards and legal recognition of digital credentials.
User Education Most people don’t understand public-private key cryptography or the risks of key loss.
Issuer Adoption Large organizations must be willing to issue verifiable credentials.
Recovery and Custody Solutions like social recovery and institutional custody are improving but not yet perfect.
The Roadmap to Replacing Traditional Logins
A realistic transition might look like this:
- 2026–2027: Passwordless login becomes default for Web3 and many consumer apps. Major platforms offer “Sign in with Decentralized Identity” options.
- 2028–2030: Governments recognize digital credentials for key services. Enterprises adopt SSI for internal and customer identity.
- 2030+: Traditional passwords become legacy systems, similar to how floppy disks or fax machines are viewed today.
The shift will likely be gradual and hybrid — many services will support both traditional and decentralized methods during the transition period.
How Individuals Can Prepare Today
- Start using Web3 wallets with strong recovery mechanisms.
- Experiment with platforms that support decentralized login (Lens, various dApps).
- Collect and manage verifiable credentials as they become available.
- Use password managers and hardware security keys as a bridge.
- Stay educated on best practices for digital identity hygiene.
How Businesses and Developers Should Act
- Integrate wallet-based authentication (SIWE — Sign-In with Ethereum) as a primary option.
- Explore issuing and accepting verifiable credentials.
- Design products with selective disclosure and privacy in mind.
- Partner with established DID infrastructure providers rather than building everything from scratch.
The Bigger Picture: A More Human Internet
Decentralized identity represents more than a technical upgrade. It’s a philosophical shift toward giving individuals greater agency over their digital lives. By moving from “you are what the platforms say you are” to “you control your own verifiable reputation,” we can build systems that are simultaneously more secure, more private, and more inclusive.
While the complete replacement of traditional logins won’t happen overnight, the momentum in 2026 is undeniable. The building blocks are in place, adoption is accelerating, and the benefits are too compelling to ignore.
The future of logging in won’t involve remembering passwords. It will involve proving truths about yourself — on your own terms, with cryptographic certainty, and without unnecessary data exposure.
By mid-2026, Decentralized Identity has transitioned from a theoretical ideal to the backbone of the Sovereign Internet. The replacement of traditional logins is not just a technical upgrade; it is a fundamental shift in the power dynamics of the web. By placing the “Root of Trust” back in the hands of the individual, DID is dismantling the data silos that have fueled the surveillance capitalism of the last two decades.
The true success of DID in 2026 lies in its simplicity. As users begin to realize that they can access the entire digital world with a single, secure, and private “Identity Hub,” the desire to maintain hundreds of separate, vulnerable accounts will evaporate. As we look toward 2027, the winners in the tech space will be those who prioritize Identity Portability, ensuring that in a world dominated by AI and automation, the human element remains verifiable, sovereign, and secure.
That future is closer than most people realize.